In my last post, Pillars of Successful Cloud Solutions – PROCESS, I discussed how processes that are well-defined, documented, and enforced at all levels significantly contribute to a successful Cloud implementation. I touched on the benefits of using an IT Steering committee that enables organizations to research, plan, and implement their technology roadmaps. In addition, I mentioned that all applications—whether on-premise or in the Cloud—require attention in five key areas: User Maintenance, Security, Patching/Upgrades, Database/System Maintenance, and Data Integrity Validation. Below is a brief definition of each key area.
User Maintenance: Adding, removing, and modifying login accounts
Security: Granting, revoking, and modifying access to the application within the application and auditing access to sensitive data/modules
Patching/Upgrades: Installing updates/service packs/patches/hotfixes/cumulative updates along with upgrading to the next or future release of the application in accordance with recommended practices outlined by the software publisher
Database/System Maintenance: Routine/Scheduled tasks and jobs recommended by the software publisher to keep the application performing at an optimum level
Data Integrity Validation: Application and/or system routines and reports that are usually scheduled to run on a predefined timetable or on demand that review the data to ensure it is accurate and up-to-date
In this post, we will look at these areas at a high level and address the age-old questions of Who, Where, When, Why, and How. Depending on the type of Cloud solution deployed, answers to those questions can vary widely.
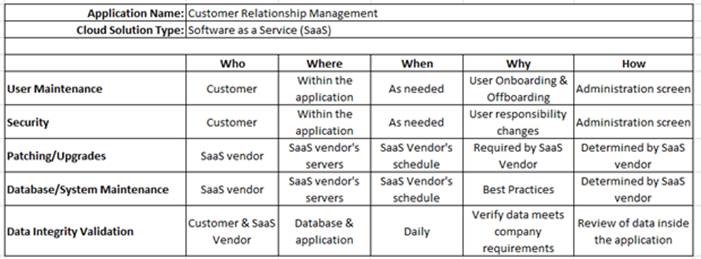
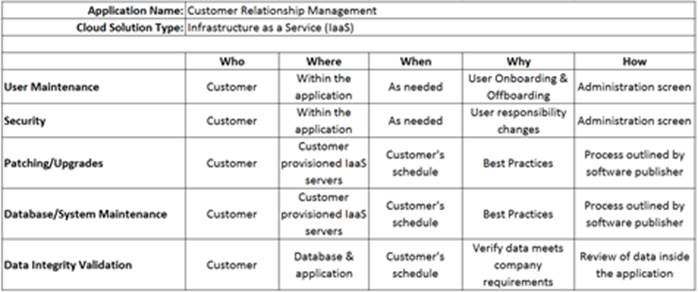
For example, let’s look at answering the “When” of Patching/Upgrades in a SaaS solution vs an IaaS solution. In the SaaS solution, updates are done on the SaaS solution provider’s schedule whereas in the IaaS solution, the customer sets the schedule.
Additionally, answering the “Who” of a cloud solution by completing a responsibilities matrix can identify gaps in coverage, reinforce task assignments to specific individuals, and provide the executive team with a quick snapshot to compare against any compliance or control standards.
To help illustrate this I have put together simplified SaaS and IaaS matrices.
SaaS Matrix for a Customer Relationship Management system:
IaaS Matrix for a Customer Relationship Management system:
One of the greatest benefits of using this type of matrix is identifying gaps in responsibilities and coverage. These key areas are part of the normal “care and feeding” of an application’s lifecycle. Those tasks that can be done by the customer would typically go to people identified as Application Administrators (see previous post called Pillars of Successful Cloud Solutions – PEOPLE).
To provide some real world context to each of these areas I have listed below some of the issues encountered when proper care and feeding is not performed.
User Maintenance: In a CRM system, former employees were not removed from the application and had access to the company’s intellectual property, customer list, pricing, and contracts, while new employees were not setup on a timely basis, impacting their ability to complete their tasks.
Security: In an ERP system, all users were setup with the same security rights (system administrator) and had access to payroll information for all employees.
Patching/Upgrades: In an ERP system, a company decided to not upgrade for eight years. By that time, the software publisher no longer supported the version owned by the company, and newer workstations with newer Operating Systems had significant issues running the program. While functionality of a more recent version of the ERP system would have reduced manual work drastically, upgrading to the current version was not an option as several upgrade jumps were required and the system could not be down for the period of time required.
Database/System Maintenance: In an ERP system, reporting, transaction processing, and patch application slowed down significantly over time as indexes were not updated, the database was not optimized, and processes creating deadlocks were not identified or addressed.
Data Integrity Validation: In a CRM system, imported customer information and sales data was not validated against the ERP system of record, mass updates to customer records were performed incorrectly, orphaned records were not identified and removed from the system, and inventory counts were not being reduced when allocated to a Sales Order.
Being vigilant in each of these areas will save you time, money, headaches, and sleepless nights. These may seem like an overwhelming set of tasks but in reality they are not. Getting started can be the most difficult part. Using a Cloud Advisor who can look at these five key areas, identify gaps, review existing processes, and generate an action plan with short-, medium-, and long-term goals will provide measureable value.
If you are interested in learning more about RSM’s Cloud Computing Rapid Assessment, check out this link.
If you are interested in learning more about RSM Management Consulting practice (help with forming an IT Steering committee), check out this link.
For more information on RSM’s offerings please check out our website. You can also contact RSM’s technology consulting professionals at 800.274.3978 or email us.

 RSMUS.com
RSMUS.com