The Borderless Datacenter |
|
Part 1 of 3 – Business Driven Infrastructure Design |
|
 |
|
|
Business leaders around the globe experience an ever increasing opportunity to expand into new markets, and increase their revenue streams from new lines of business. This is especially true in the middle market sized organization, and while this can be great for the business overall it can also have an unintended impact to the IT function. Especially in scenarios where several key infrastructure components are facing upgrades or in some other way not capable to scale with the business. IT managers often are challenged to extend the range of existing infrastructure while at the same time keeping up with the maintenance required to ensure reliable access to (and the security of) corporate data and trade secrets. This can lead to costly projects that get abandoned or improperly deployed, which has a direct impact on the ability for the business to grow. Not to mention that it also creates a drag on the operational efficiency of the business. |
|
Digital transformation is now viewed as a key component to maintaining a competitive advantage in today’s marketplace! |
|
The Changing Face of Corporate Data |
|
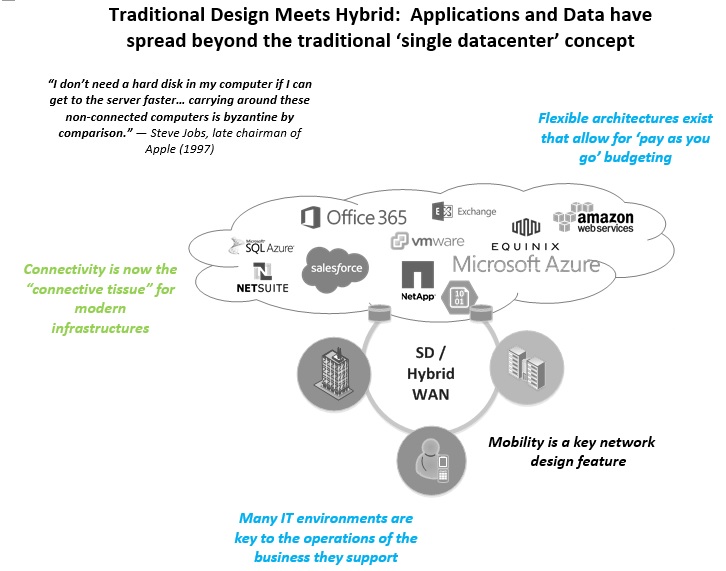
Fact: The traditional datacenter design is no longer feasible. |
|
|
Along with the many challenges that IT Managers face in keeping the IT lights on from day to day, there are now new factors that need to be addressed. On top of this, many of the typical functions that IT has traditionally performed have now become business critical, with serious impacts to the business when many of the systems maintained by the IT function are not operational. |
|
Datacenter GeoAs businesses in the middle market grow and expand, the geographical footprint expands with it. IT Managers struggle to extend corporate data to be close to users. Cloud DataCorporate data solutions are becoming increasingly cloud enabled and/or cloud only. This element of corporate data is a struggle because IT Managers lose some control over elements of critical systems. MobilityAs corporate data users become more sophisticated, and the next generation workforce demand flexibility in how they consume network services, mobility has become a center point of IT environments rather than a feature of it. |
Operational ImpactWhen the business performs any type of business continuity planning or testing, one of the big takeaways is the realization of just how many dependencies key business units have on IT. Cost Measurement In the traditional datacenter design, where many IT expenses were capital in nature, ROI was easy to measure. The new era of IT will include more than half of data and systems being housed as an “as a service” model. IT Managers will need to change how they capture and track costs across the enterprise. Especially when tracking costs back to operational units and geographical locations. |
 |
|

|
Maximizing your investment in technology requires a grasp of the big picture without losing sight of the smallest details.Our technology team is focused on ensuring that you have the right technology, properly installed and managed, to deliver the functionality and ease of use to your employees. As your business grows, so do your technology and regulatory challenges. To meet these demands, many organizations are turning to secure, flexible cloud solutions to house some or all of their IT infrastructure. The RSM Cloud Portfolio includes services to help increase your efficiency and ensure you get the most from your technology investments. We understand the road to cloud success can be full of complicated choices, and many organizations have trouble identifying the best cloud solution for them. Check out our cloud journey E-Book! |
IT Strategy, With Security In Mind |
|
With today’s advanced threats, rapidly changing malware and a constantly shifting legal and regulatory landscape, it is essential to clearly understand the risks associated with your IT assets. While a third party may already be conducting your security testing, it might be time for a new perspective—because not all IT security testing is the same. |
|
In the current economic, political, and social landscape, addressing security has become a core necessity for most organizations:
|
|
IT Strategy Checklist
|
|
Find the right partnerAt RSM, we understand what’s required for people, processes and technology to effectively interact so your organization’s strategic goals can be met. Technology is instrumental in driving business growth and creating more efficient processes that contribute to increased productivity. We take the time to understand how your business operates, we know how to ask the right questions and we listen, so we can help you solve your business challenges based on the specific needs of your business and industry. By combining technical knowledge and business savvy with our full range of IT services, we’re able to assess complex situations, devise effective solutions, and implement them for you quickly and cost effectively. Our technology and management consulting professionals average 15+ years of technical experience, with deep industry knowledge. We’re well versed in the latest IT solutions and consistently receive industry recognition. Our Security and Privacy practice is well versed in dealing with even the most complex security challenges. Every day, they are helping organizations identify and implement the right level of controls to align with their business goals and protect your sensitive data. Across each of the main risk areas—oversight, people, process and technology—we work with your organization to identify the risks, protect against the threats those risks pose. They also will detect tactical and strategic issues, helping you create a response plan, and develop effective strategies for recovery after an incident. |
|
|
|
|

 RSMUS.com
RSMUS.com